The Offshore Security Playbook: How CTOs Protect IP and Data Without Killing Development Velocity

The average data breach cost $4.88 million in 2024. That’s not a typo. That’s the price tag IBM reports for a single security incident—and it’s been climbing year after year. For CTOs managing offshore teams, there’s a brutal tension: your developers need access to code, data, and systems to build anything meaningful, but every open door is a potential breach vector.
Offshore teams have become essential for scaling development. But they also expand your attack surface in ways most CTOs handle with friction, not frameworks. You either lock everything down and kill your development velocity, or you trust blindly and accept the risk. That’s the false choice—and it’s costing companies millions.
The 3 Real Threats (Not What You Think)
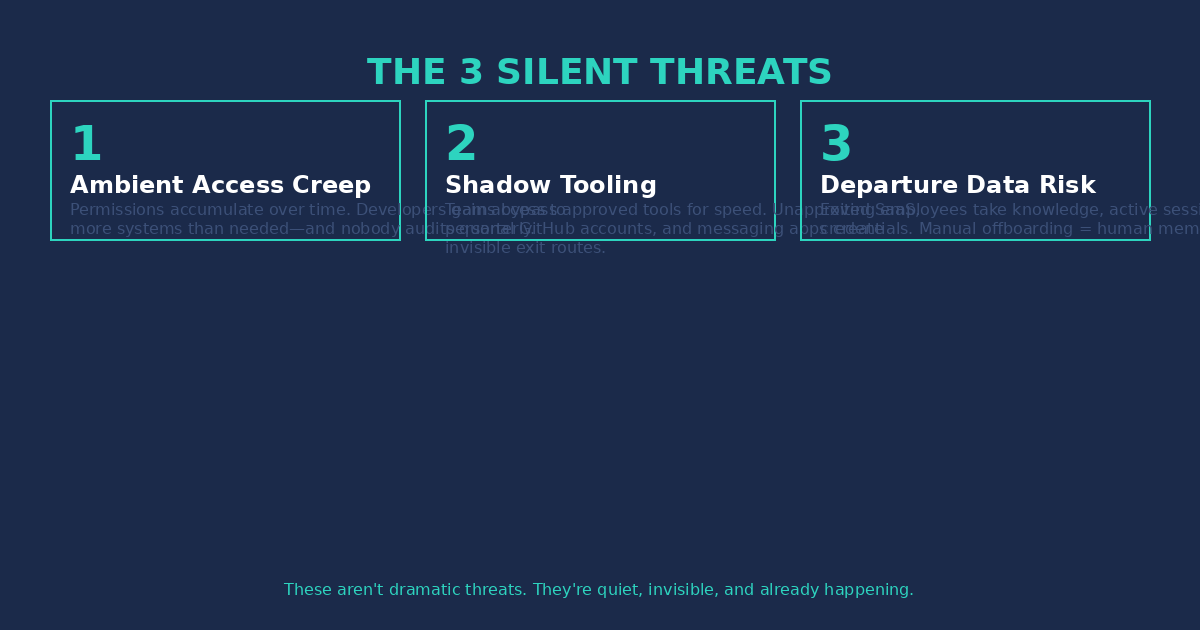
Most CTOs worry about external hackers, sophisticated attacks, nation-state actors. But the three biggest threats to your offshore development are already inside your operation:
Threat 1: Ambient Access Creep
Developers accumulate permissions over time. They get access to repositories for Project A, then Project B, then the production database “just for debugging.” Nobody audits these permissions quarterly. A developer who joined to build feature X now has access to your entire intellectual property—and nobody’s checking if they still need it.
Threat 2: Shadow Tooling
Your offshore team needs to move fast. When your approved tools slow them down, they find workarounds—unapproved SaaS for file sharing, personal GitHub accounts for code, messaging apps that don’t log anything. You can’t secure what you don’t know exists. Shadow tooling is how sensitive data walks out the door through channels you don’t monitor.
Threat 3: Departure Data Risk
When contractors or full-time employees leave, they take knowledge. That’s expected. But they also take access—active sessions, cached credentials, downloaded repositories. If your offboarding is reactive instead of automated, you’re relying on human memory to revoke access. And humans forget.
These aren’t dramatic threats. They’re quiet, invisible, and already happening in most offshore operations. The question isn’t whether they exist—it’s whether you have a framework to manage them.
The Security-Velocity Matrix
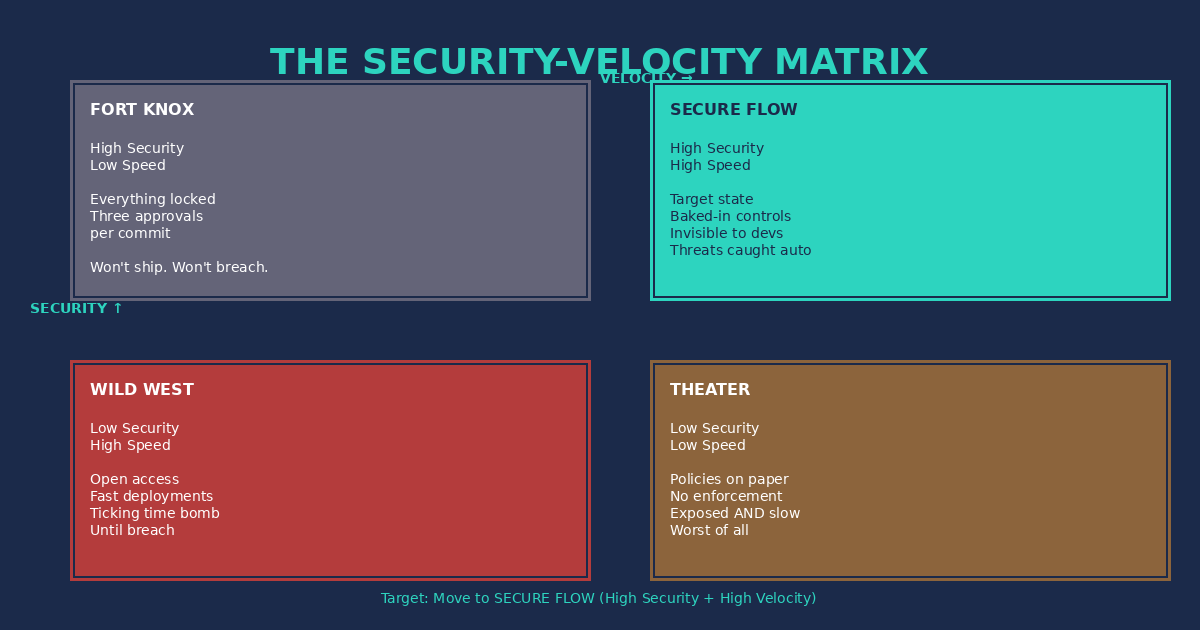
Every CTO is trying to find the right balance between security and development speed. Here’s how to think about it:
Quadrant 1: Fort Knox (High Security, Low Speed)
Everything is locked down. Every commit requires three approvals. Developers spend more time in security theater than writing code. You won’t get breached—but you also won’t ship anything.
Quadrant 2: Wild West (Low Security, High Speed)
Open access, fast deployments, maximum velocity. Until the breach happens. This is where most startups with offshore teams live—and it’s a ticking time bomb.
Quadrant 3: Security Theater (Low Both)
You have security policies on paper, but no enforcement. No monitoring. No actual protection. You’re exposed AND slow. The worst of all worlds.
Quadrant 4: Secure Flow (High Both)
This is the target. Security is baked into your processes so deeply that it becomes invisible. Developers don’t notice it—they just work. Threats are caught automatically. Access is managed without manual review. This is where you want to live.
The 8-Point Offshore Security Framework

Here’s the framework that gets you to Secure Flow:
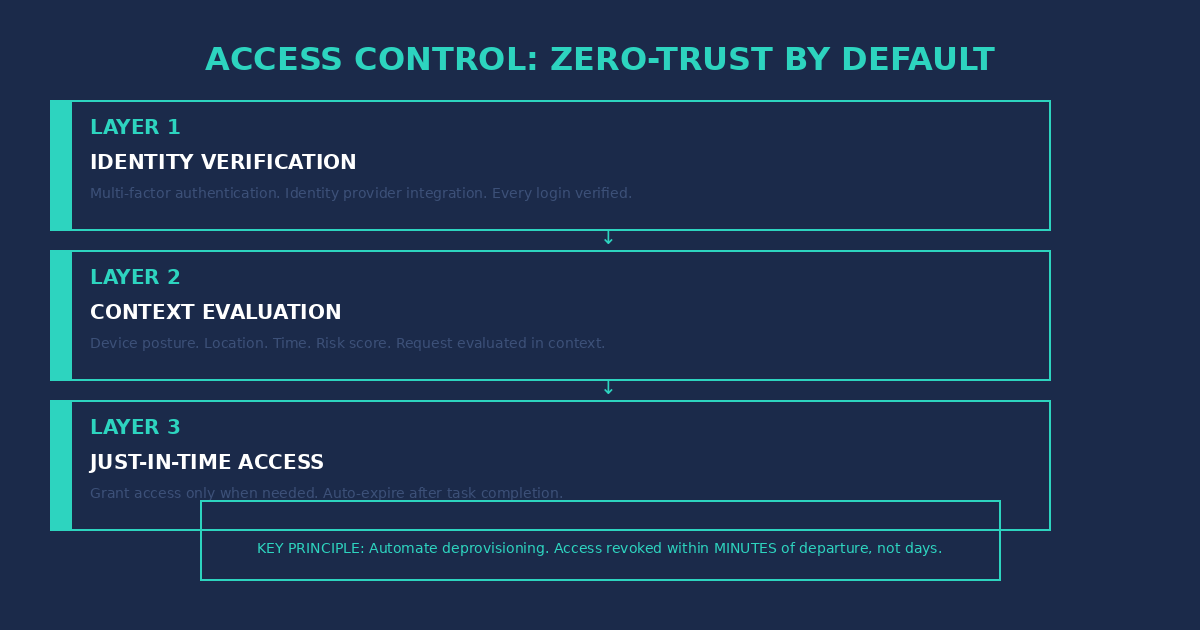
1. Access Control: Zero-Trust by Default
Never trust, always verify. Every request for access is evaluated fresh. Implement automated provisioning and—critically—automated deprovisioning. When someone leaves, their access should be revoked within minutes, not days.
2. Code Security: Branch Protection + Secret Scanning
Require pull request reviews before merging. Block direct commits to main. Run automated secret scanning on every push—detect API keys, passwords, and credentials before they ever reach your repository. Enforce signed commits so you know exactly who wrote every line.

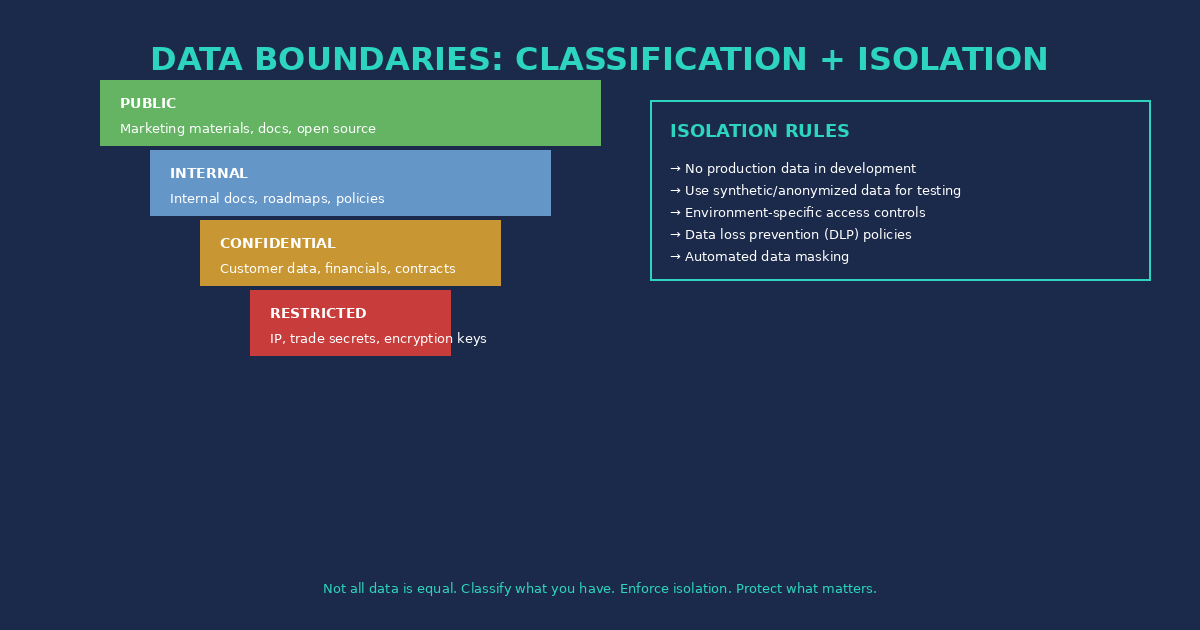
3. Data Boundaries: Classification + Isolation
Not all data is equal. Classify what you have (public, internal, confidential, restricted). Then enforce isolation: no production data in development environments. Ever. Use synthetic or anonymized data for testing.
4. Monitoring: Audit Logging + Anomaly Detection
Log everything that matters—access events, code commits, data exports, permission changes. But don’t just log: detect anomalies. Someone downloading a full database at 2 AM? That’s not surveillance; that’s protection. Build alerts for the signals that actually matter.
5. Device Security: Endpoint Protection
If your offshore team works on personal machines, you have a problem. Enforce minimum security requirements: disk encryption, up-to-date OS, approved antivirus. Consider MDM solutions for company-owned devices.
6. Communication Security: Approved Channels Only
Define which tools are approved for work communication—and enforce it. Encrypted messaging, approved email, documented Slack channels. Train your team on what’s acceptable and what isn’t.
7. Vendor Risk: Extend Your Framework
Your offshore team might use subcontractors or their own vendors. Your security framework needs to extend to them. Minimum security requirements in contracts, right-to-audit clauses, regular assessments.
8. Incident Response: Plan for Failure
Assume breaches will happen. Have a documented incident response plan. Know who to call, what to contain, how to communicate. Practice it. A plan you haven’t tested is just a document.
Implementation Without the Friction
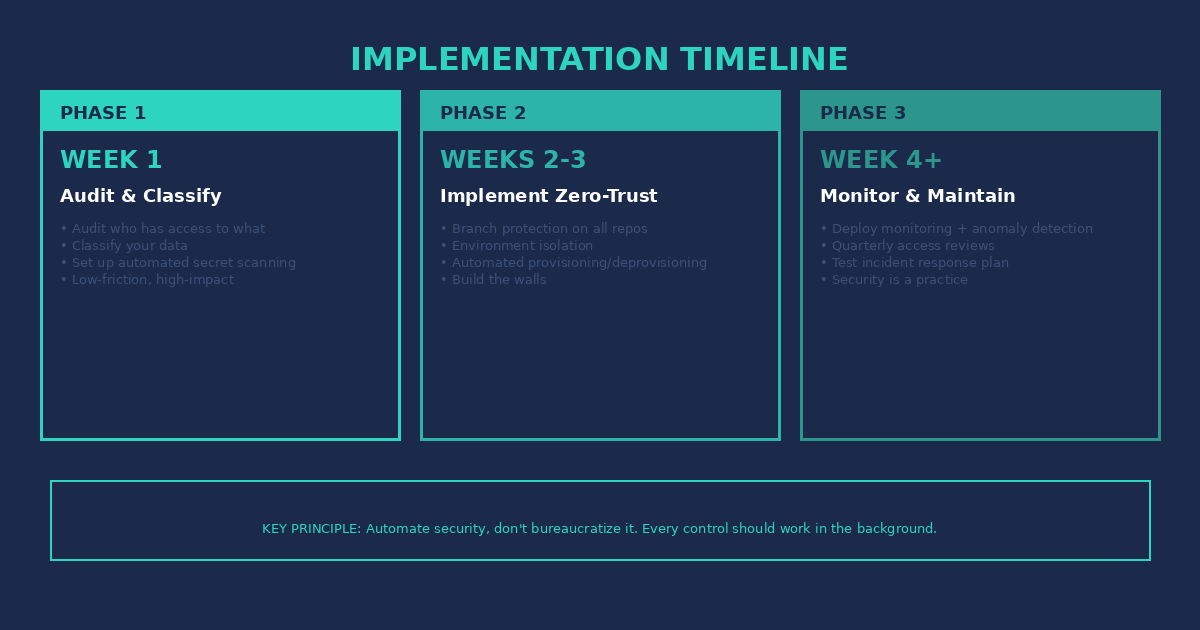
You don’t need to implement everything at once. Here’s a phased approach:
Phase 1 (Week 1): Audit and Classify
Audit who has access to what. Classify your data. Set up automated secret scanning on your repositories. This is low-friction, high-impact work that gives you visibility.
Phase 2 (Week 2-3): Implement Zero-Trust and Isolation
Implement branch protection on all repositories. Set up environment isolation—no prod data in dev. Start automated provisioning and deprovisioning. This is where you build the walls.
Phase 3 (Week 4+): Monitor and Maintain
Deploy monitoring and anomaly detection. Establish a quarterly access review cadence. Test your incident response plan. Security isn’t a project; it’s a practice.
The key principle: automate security, don’t bureaucratize it. Every control should work in the background. If your developers notice it, you’ve made it too complicated.
The ROI of Getting This Right
Here’s the business case: implementing a security framework costs tens of thousands of dollars. A data breach costs millions. The math is brutal and simple.
Companies with security frameworks experience 50% lower breach costs than those without. That’s not theory—that’s IBM’s data. Beyond breach costs, you get insurance premium reductions, client trust that wins deals, and compliance readiness that opens enterprise markets.
Security isn’t a cost center. It’s a competitive advantage that pays for itself.
Ready to Secure Your Offshore Operations?
At GTCatalyst, we help CTOs implement the Offshore Security Framework without killing development velocity. Our Cybersecurity Fortification service gives you a complete security posture assessment—we find the gaps, build the plan, and implement the controls.
Start with a free security posture assessment. We’ll audit your current state, identify your critical gaps, and give you a roadmap to Secure Flow.
Don’t wait for a breach to take security seriously. The $4.88 million question is whether you can afford not to.